Client Advisory: Active Phishing Campaigns Impersonating FINRA and the SEC
If your firm is registered with FINRA, the SEC, SIPC, or the New York Department of Financial Services, you need to act on this immediately. Beginning March 26, 2026, a coordinated phishing campaign began targeting broker-dealers, investment advisers, and other financial services firms with fraudulent emails designed to impersonate FINRA and SEC staff. FINRA has issued a formal Cybersecurity Alert confirming the campaign is active and ongoing.
This is not a theoretical risk. Multiple firms have already reported receiving these messages. The goal is to deceive employees into engaging with threat actors -- potentially through AI-powered video calls that can realistically impersonate regulatory staff. Your employees need to know about this today.
How the Attack Works
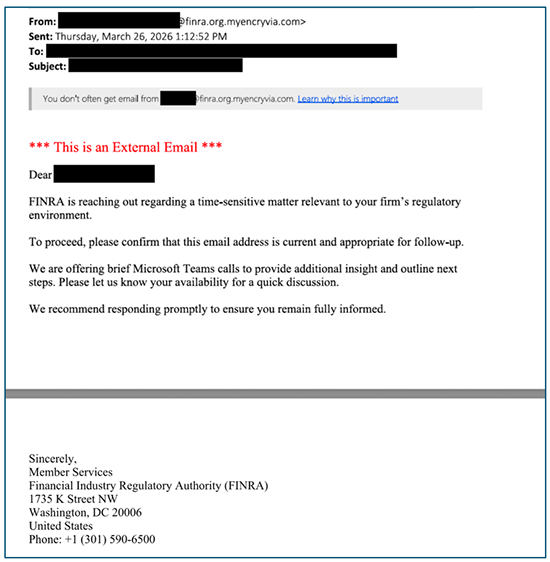
The emails in this campaign share a consistent pattern, even as the specific wording varies across targets. Here is what to watch for:
Spoofed sending domains: The emails originate from domains that mimic legitimate regulatory addresses but are not. FINRA-spoofed emails have been traced to finra[.]org[.]getencryvia[.]com and finra[.]org[.]myencryvia[.]com (brackets added intentionally to prevent accidental clicks). Legitimate FINRA emails will only ever come from the @finra.org domain. The same pattern applies to SEC communications -- look for additional domains appended after the legitimate .gov address.
Urgency framing: Subject lines reference the firm by name and describe a time-sensitive matter relevant to your firm's regulatory environment -- designed to trigger an immediate response without careful scrutiny.
Two-stage trust building: Recipients are first asked to reply and confirm their email address to enable secure communications, followed by a request to schedule a Microsoft Teams call with the purported FINRA or SEC contact. Each step builds perceived legitimacy before the real ask is made.
AI-powered impersonation risk: The Teams call request is particularly concerning. Threat actors may use AI-generated deepfakes or voice synthesis to convincingly impersonate a real FINRA or SEC employee during the call. Do not assume that seeing or hearing someone on video is sufficient verification of their identity.
What Your Employees Should Do Right Now
If anyone at your firm receives an unexpected email claiming to be from FINRA, the SEC, or another regulator:
Do not click any links or open any attachments. Escalate to your IT team immediately.
Do not reply to the email. Any response, even a simple acknowledgment, validates your address to the attacker.
Do not accept or join unexpected meeting requests. Be especially skeptical of Teams calls arranged via email from an unverified sender.
Verify independently. If you believe the email may be legitimate, contact the regulator using contact information from their official website -- not from the email itself. FINRA contacts are available at finra.org; SEC contacts are at sec.gov.
Escalate and report. Alert InnerCircle and/or your IT personnel and report the phishing attempt. Incidents can also be reported to FINRA, to CISA at report@cisa.gov or 888-282-0870, or to the FBI's Internet Crime Complaint Center at IC3.gov.
Broader Email Security Reminders for All Staff
This campaign is a timely reminder to reinforce foundational security habits across your organization. All employees should be reminded to:
Never trust the From display name alone. Always inspect the actual sending email address.
Be cautious of alarmist or urgent subject lines such as urgent, action required, transfer, or request.
Avoid downloading attachments from unsolicited senders.
Use bookmarked URLs to navigate to frequently visited websites instead of following links in email.
Call back using a number already on file -- not one provided in the suspicious email -- to validate any unusual request.
Contact IT whenever there is doubt about an email's authenticity.
Known Malicious Domains -- Block These Now
InnerCircle is proactively blocking the following domains at customer email gateway and firewall levels, and is monitoring network traffic for any activity related to these domains:
finra[.]org[.]getencryvia[.]com
finra[.]org[.]myencryvia[.]com
FINRA has reported these domains to their registrar and hosting provider for suspension. Additional variants should be anticipated. Threat actors routinely rotate domains, sender names, and subject lines as campaigns evolve -- maintain vigilance even after initial blocking is in place.
Why This Campaign Is Different: The AI Factor
What distinguishes this campaign from prior phishing attempts is the deliberate use of AI-enhanced impersonation at the point of live interaction. Soliciting a Teams call is not incidental -- it is tactical. Once connected, a threat actor using AI voice synthesis or deepfake video technology could convincingly impersonate a government official and request sensitive firm data, login credentials, or other information that would normally require in-person or out-of-band verification.
Employees should understand that hearing a voice or seeing a face on a video call is no longer a reliable identity verification method. Any unexpected meeting request from a regulatory body should be validated through a separate, pre-established communication channel before anyone joins the call.
How InnerCircle Can Help
We are actively monitoring this threat and are available to assist clients who need help responding. Whether your firm has already received one of these emails, needs help blocking the malicious domains, or wants to run a targeted awareness exercise for staff, reach out to us directly.
Our security service offerings -- Secure Core, Secure Core Plus, Secure Edge, and Active Arc -- are built to address exactly this type of threat, with layered defenses that include:
Advanced email filtering to intercept lookalike and spoofed sending domains before they reach employee inboxes.
Phishing simulation and security awareness training to build employee resilience against social engineering tactics.
Managed Detection and Response (MDR) to detect and contain threats quickly if something does get through your perimeter.
Policy and compliance support to ensure your incident response procedures are current and tested before you need them.
Do not wait for an incident to surface. Contact InnerCircle today to make sure your firm is protected.
Official References and Further Reading
The following official sources confirm and provide additional detail on this active campaign:
FINRA Cybersecurity Alert: Ongoing Phishing Campaign Impersonating FINRA Employees (March 26, 2026)
FBI Internet Crime Complaint Center (IC3): File a Cybercrime Complaint
This advisory is provided for informational purposes to clients and contacts of InnerCircle Technology Advisors. It is based on publicly available information and official regulatory alerts.